Miloserdov Alternatives & Competitors
Ethical hacking and penetration testing - InfoSec, IT, Kali Linux, BlackArch.
Alternatives & competitors to miloserdov.org in terms of content, traffic and structure
KaliTut Linux and pentesting blog - KaliTut.
World's fastest and most advanced password recovery utility
Welcome!.
Aircrack-ng.
OnlineHashCrack is a Professional Cloud Password Testing and Recovery Services ensuring ethical practices for cybersecurity experts, for MD5 NTLM Wordpress Joomla SHA1 MySQL OSX WPA, PMKID, Office Docs
Home of Kali Linux, an Advanced Penetration Testing Linux distribution used for Penetration Testing, Ethical Hacking and network security assessments.
A blog dedicated to sharing actionable Kali Linux tutorials, guides, cheatsheets, and tips and tricks.
Best Place for Kali Linux Tutorials. Large number of articles on Kali Linux in easy steps from basic to advanced. Command by command with screenshots.
Decrypt and crack your MD5, SHA1, SHA256, MySQL, MD5 Email, SHA256 Email, and NTLM hashes for free online. We also support Bcrypt, SHA512, Wordpress and many more.
Just a moment...
Information Security software for open computing environments, related publications, and professional services
Crackstation is the most effective hash cracking service. We crack: MD5, SHA1, SHA2, WPA, and much more...
Pentest-Tools.com is a cloud-based toolkit for offensive security testing, focused on web applications and network penetration testing.
Nmmapper offers nmap scans,9 subdomain finder tools,theHarvester,wappalyzer,whatweb online
Kismet is a sniffer, WIDS, and wardriving tool for Wi-Fi, Bluetooth, Zigbee, RF, and more, which runs on Linux and macOS
Gpuhash.me is ranked number 10M in the world and links to network IP address 5.2.73.234.
Stanev.org network crosspoint.
Oracle VM VirtualBox .
The Exploit Database - Exploits, Shellcode, 0days, Remote Exploits, Local Exploits, Web Apps, Vulnerability Reports, Security Articles, Tutorials and more.
Wonder How To is your guide to free how to videos on the Web. Search, Browse and Discover the best how to videos across the web using the largest how to video index on the web. Watch the best online video instructions, tutorials, & How-Tos for free. Have your own how to videos? Submit them to share with the world.
Build cyber workforce resilience with our unmatched skills development and hands-on learning platform and library.
LinuxConfig.org
Wifigeeks.org is ranked number 10M in the world and links to network IP address 104.27.182.196.
Kali Linux tutorials is an independent platform that covers step by tutorials, advanced penetration testing, Ethical Hacking and network security tools.
Decrypter et encrypter les hashs MD5 en ligne.
Welcome to the Openwall Community Wiki! [Openwall Community Wiki] .
Information Security software for open computing environments, related publications, and professional services
Hash, hashing, and encryption toolkit.
Attention Required! | Cloudflare.
Raj Chandel's Blog
Welcome to the project designed to md5 decrypt, This website contains the largest database in the world. We have a total of just over 20.408 trillion unique hashes.
Welcome - NovaSense Threat Feeds.
Error 520: Website not authorized on OVH CDN.
Telcodb.net is ranked number 10M in the world.
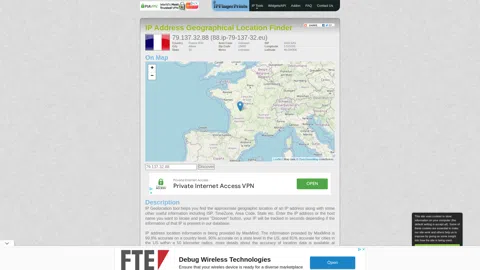
Find the location of an IP Address on map.
Online Vulnerability Scanners to map the attack surface and identify vulnerabilities. 28 trusted open source security scanners and network tools.
Comprehensive cyber security platform that provides everyone with the most effective solutions for their security requirements.
Spyse.com is ranked number 1477397 in the world and links to network IP address 5.79.90.59.
Advanced Port Scanner is a free port scanner allowing you to quickly find open ports on network computers and retrieve versions of programs running on the detected ports
Openmaniak.com is ranked number 1193913 in the world and links to network IP address 128.65.195.129.
Find dns records in order to identify the Internet footprint of an organization. Recon that enables deeper security assessments and discovery of the attack surface.