Beyondtrust Альтернативы & Конкуренты
Unwanted remote access, stolen credentials, and misused privileges threaten every organization. BeyondTrust offers the industry’s broadest set of privileged access management capabilities to defend against cyber attacks. Our Privileged Access Management platform provides visibility and control over all privileged accounts, users, and access. Trusted by more than 20,000 companies and counting.
Альтернативы и конкуренты beyondtrust.com по содержанию, трафику и структуре
Get the most complete Identity Security and Access Management Solutions that enable secure access across any device, anywhere, at just the right time.
Thycotic is now Delinea, a PAM leader providing seamless security for modern, hybrid enterprises. With Delinea, privileged access is more accessible.
Tenable enables security teams to focus on the vulnerabilities and assets that matter most. From Cloud to OT, gain full visibility of the modern attack surface.
Access Denied.
4sysops – For SysAdmins and DevOps.
Dark Reading: Connecting The Cybersecurity Community.
Level up SecOps with the only endpoint to cloud, unified cybersecurity platform. Confidently act to prevent breaches with a leading MDR partner. Request demo!
One of the most full-featured privileged access management (PAM) solutions available is easy to use, well adopted, and affordable. Free trial.
How long it would take a computer to crack your password?
Simply secure identity and access for digital and industrial environments
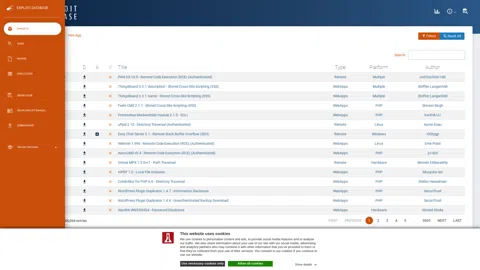
The Exploit Database - Exploits, Shellcode, 0days, Remote Exploits, Local Exploits, Web Apps, Vulnerability Reports, Security Articles, Tutorials and more.
Discover how Qualys helps your business measure & eliminate cyber threats through a host of cybersecurity detection & remediation tools. Try it today!
CVEdetails.com is a free CVE security vulnerability database/information source. You can view CVE vulnerability details, exploits, references, metasploit modules, full list of vulnerable products and cvss score reports and vulnerability trends over time
The MITRE Corporation.
CrowdStrike is a global cybersecurity leader with an advanced cloud-native platform for protecting endpoints, cloud workloads, identities and data.
La référence dans la cybersécurité : avec plus de 60 formations dans tous les domaines de pratique, SANS forme plus de 40 000 professionnels cyber par an.
NCSC.
CIS is a forward-thinking nonprofit that harnesses the power of a global IT community to safeguard public and private organizations against cyber threats.
Welcome to the Petri IT Knowledgebase, the trusted resource for IT Professionals for more than 20 years.
Get database management and data modeling tools to monitor, secure, and improve data systems with confidence–whether in the cloud or on-premises.
Tips for configuring Windows Server 2012, also Exchange 2010 and Windows 8. Computer Performance for advice on creating PowerShell and Logon Scripts.
The independent online home for Windows IT professionals and those seeking or holding Microsoft's certifications.
IT knowledge base for system administrators
Build cyber workforce resilience with our unmatched skills development and hands-on learning platform and library.
SecurityWeek provides cybersecurity news and information to global enterprises, with expert insights & analysis for IT security professionals
Threatpost, is an independent news site which is a leading source of information about IT and business security for hundreds of thousands of professionals worldwide.
Cybersecurity news with a focus on enterprise security. Discover what matters in the world of information security today.
The essential resource for cybersecurity professionals, delivering in-depth, unbiased news, analysis and perspective to keep the community informed, educated and enlightened about the market.
CSO offers the latest information and best practices on business continuity and data protection, best practices for prevention of social engineering scams, malware and breaches, and tips and advice abut security careers and leadership.
Experts in Privileged Access Management, secure automation, and endpoint management using PAM, PPA, and PEM. Cyber security fundamentals to protect your IT systems from attacks.
DNS resolution error | www.passwordmeter.com | Cloudflare.
Unwanted remote access, stolen credentials, and misused privileges threaten every organization. BeyondTrust offers the industry’s broadest set of privileged access management capabilities to defend against cyber attacks. Our Privileged Access Management platform provides visibility and control over all privileged accounts, users, and access. Trusted by more than 20,000 companies and counting.
ARCON| PAM enforces Just-in-Time access and offers the most robust session management engine to safeguard business and infrastructure assets spread across hybrid environments from insider and third-party threats.
Provide secure identity and access management and single sign-on to all applications from any device
Security.org simplifies home security and personal safety. Using cutting-edge research, our experts educate and inspire people to stay safe.
How strong are your passwords? Test how secure they are using the My1Login Password Strength Test.
Number one vulnerability management and threat intelligence platform documenting and explaining vulnerabilities since 1970.
Bringing you the best SSL/TLS and PKI testing tools and documentation.
Attention Required! | Cloudflare.
Information Security Services, News, Files, Tools, Exploits, Advisories and Whitepapers
Actionable vulnerability intelligence for every company.
NIST promotes U.S. innovation and industrial competitiveness by advancing measurement science, standards, and technology in ways that enhance economic security and improve our quality of life.
OWASP Foundation, the Open Source Foundation for Application Security on the main website for The OWASP Foundation. OWASP is a nonprofit foundation that works to improve the security of software.
PortSwigger offers tools for web application security, testing, & scanning. Choose from a range of security tools, & identify the very latest vulnerabilities.
Acunetix is an end-to-end web security scanner that offers a 360 view of an organization’s security. Allowing you to take control of the security of all you web applications, web services, and APIs to ensure long-term protection. Acunetix’s scanning engine is globally known and trusted for its unbeatable speed and precision.
GIAC Certifications develops and administers premier, professional information security certifications. More than 30 certifications align with SANS training and ensure mastery in critical, specialized InfoSec domains. GIAC certifications provide the highest and most rigorous assurance of cyber security knowledge and skill available to industry, government, and military clients across the world.
Role-based content to prepare for exams, certifications, or to train your entire workforce.