Mandiant Alternative & Concorrenti
Threat Intelligence Solutions. Mandiant is recognized as the leader in threat intelligence with expertise gained on the frontlines of cyber security.
Alternative e concorrenti a mandiant.com in termini di contenuto, traffico e struttura
.
CrowdStrike is a global cybersecurity leader with an advanced cloud-native platform for protecting endpoints, cloud workloads, identities and data.
Recorded Future is the most comprehensive and independent threat intelligence platform. Identify and mitigate threats across cyber, supply-chain, physical and fraud domains.
Latest News.
The MITRE Corporation.
FortiGuard.
Digital Attack Map - DDoS attacks around the globe
Achieve next-gen visibility with NETSCOUT's Visibility Without Borders network, security, and application performance monitoring platform. Unleash your unstoppable enterprise.
Check Point Infinity architecture delivers consolidated Gen V cyber security across networks, cloud, and mobile environments.
Access Denied.
SentinelOne réunit la protection des endpoints, du cloud, de l’identité et des données. Enrichi par notre Security Data Lake, votre expérience de cybersécurité sera fluide et efficace.
Palo Alto Networks enables your team to prevent successful cyberattacks with an automated approach that delivers consistent security across cloud, network and mobile.
Level up SecOps with the only endpoint to cloud, unified cybersecurity platform. Confidently act to prevent breaches with a leading MDR partner. Request demo!
Anomali is a security operations platform harnessing the power of AI to deliver breakthrough threat detection, visibility and cyber exposure management.
Learn how we enable cyber threat intelligence, security operations, and cyber risk teams to act on the highest fidelity intelligence and automate processes. Get a demo.
The first threat intelligence platform purpose-built for Security Operations to prioritize, automate and collaborate for TDIR.
Meet your business challenges head on with cloud computing services from Google, including data management, hybrid & multi-cloud, and AI & ML.
SADA is a premier cloud solutions provider specializing in technology consulting, IT services, application development, and managed services.
Meet your business challenges head on with cloud computing services from Google, including data management, hybrid & multi-cloud, and AI & ML.
Cloudonair.withgoogle.com is ranked number 10M in the world and links to network IP address 216.58.204.145.
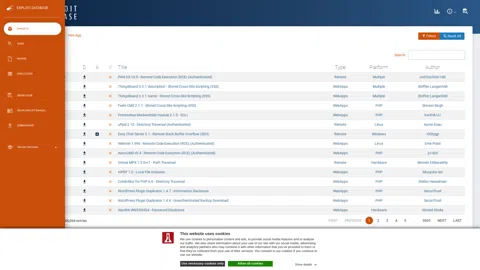
The Exploit Database - Exploits, Shellcode, 0days, Remote Exploits, Local Exploits, Web Apps, Vulnerability Reports, Security Articles, Tutorials and more.
CVEdetails.com is a free CVE security vulnerability database/information source. You can view CVE vulnerability details, exploits, references, metasploit modules, full list of vulnerable products and cvss score reports and vulnerability trends over time
OWASP Foundation, the Open Source Foundation for Application Security on the main website for The OWASP Foundation. OWASP is a nonprofit foundation that works to improve the security of software.
PortSwigger offers tools for web application security, testing, & scanning. Choose from a range of security tools, & identify the very latest vulnerabilities.
NIST promotes U.S. innovation and industrial competitiveness by advancing measurement science, standards, and technology in ways that enhance economic security and improve our quality of life.
Just a moment...
Norsenet.com is ranked number 10M in the world and links to network IP address 54.192.144.57.
Buying Guides 2022
Fortinet delivers award-winning cyber security solutions across the entire digital attack surface, securing devices, data, and applications from the data center to the cloud to the home office.
CPUG: The Check Point User Group
Number one vulnerability management and threat intelligence platform documenting and explaining vulnerabilities since 1970.
Fortinet GURU | FortiGate Guides and MORE!.
A10 Networks: Security solutions, threat intelligence, infrastructure, and application delivery for enterprises and service providers for on-premises, multi cloud, and edge cloud.
Cynet’s end-to-end, natively automated XDR platform was purpose-built to enable lean IT security teams to easily achieve comprehensive, effective protection regardless of their resources.
ShieldSquare Block.
Log Analysis / Log Management by Loggly: the world's most popular log analysis & monitoring in the cloud. Free trial. See why ⅓ of the Fortune 500 use us!
La référence dans la cybersécurité : avec plus de 60 formations dans tous les domaines de pratique, SANS forme plus de 40 000 professionnels cyber par an.
CIS is a forward-thinking nonprofit that harnesses the power of a global IT community to safeguard public and private organizations against cyber threats.
EclecticIQ develops analyst-centric products and solutions that align our clients’ cybersecurity focus with their threat reality.
F5 application services ensure that applications are always secure and perform the way they should—in any environment and on any device.
STIX - Structured Threat Information Expression (Archive) | STIX Project Documentation.
Juniper Networks dramatically simplifies network operations and driving super experiences for end users. Our solutions deliver industry-leading insight, automation, security and AI to drive real business results. We believe that powering connections will bring us closer together while empowering us to solve the world’s greatest challenges.
D3 Security's Incident Response Platform Helps Organizations Prepare For Threats & Orchestrate Security Response. Discover The Leading Solution Now
Build cyber workforce resilience with our unmatched skills development and hands-on learning platform and library.
Tenable enables security teams to focus on the vulnerabilities and assets that matter most. From Cloud to OT, gain full visibility of the modern attack surface.
Chronicle, powered by Google infrastructure, enables cost-effective use of security telemetry to improve SOC productivity and combat modern threats.